IObit Uninstaller 8.6.0.6 Archives
Drive-by Compromise AppleScript .bash_profile and .bashrc Access Token Manipulation Access Token Manipulation Account Manipulation Account Discovery AppleScript Audio Capture Commonly Used Port Automated Exfiltration Data Destruction Exploit Public-Facing Application CMSTP Accessibility Features Accessibility Features Binary Padding Bash History Application Window Discovery Application Deployment Software Automated Collection Communication Through Removable Media Data Compressed Data Encrypted for Impact External Remote Services Command-Line Interface Account Manipulation AppCert DLLs BITS Jobs Brute Force Browser Bookmark Discovery Distributed Component Object Model Clipboard Data Connection Proxy Data Encrypted Defacement Hardware Additions Compiled HTML File AppCert DLLs AppInit DLLs Bypass User Account Control Credential Dumping Domain Trust Discovery Exploitation of Remote Services Data from Information Repositories Custom Command and Control Protocol Data Transfer Size Limits Disk Content Wipe Replication Through Removable Media Control Panel Items AppInit DLLs Application Shimming Clear Command History Credentials in Files File and Directory Discovery Logon Scripts Data from Local System Custom Cryptographic Protocol Exfiltration Over Alternative Protocol Disk Structure Wipe Spearphishing Attachment Dynamic Data Exchange Application Shimming Bypass User Account Control CMSTP Credentials in Registry Network Service Scanning Pass the Hash Data from Network Shared Drive Data Encoding Exfiltration Over Command and Control Channel Endpoint Denial of Service Spearphishing Link Execution through API Authentication Package DLL Search Order Hijacking Code Signing Exploitation for Credential Access Network Share Discovery Pass the Ticket Data from Removable Media Data Obfuscation Exfiltration Over Other Network Medium Firmware Corruption Spearphishing via Service Execution through Module Load BITS Jobs Dylib Hijacking Compile After Delivery Forced Authentication Network Sniffing Remote Desktop Protocol Data Staged Domain Fronting Exfiltration Over Physical Medium Inhibit System Recovery Supply Chain Compromise Exploitation for Client Execution Bootkit Exploitation for Privilege Escalation Compiled HTML File Hooking Password Policy Discovery Remote File Copy Email Collection Domain Generation Algorithms Scheduled Transfer Network Denial of Service Trusted Relationship Graphical User Interface Browser Extensions Extra Window Memory Injection Component Firmware Input Capture Peripheral Device Discovery Remote Services Input Capture Fallback Channels Resource Hijacking Valid Accounts InstallUtil Change Default File Association File System Permissions Weakness Component Object Model Hijacking Input Prompt Permission Groups Discovery Replication Through Removable Media Man in the Browser Multi-hop Proxy Runtime Data Manipulation Launchctl Component Firmware Hooking Control Panel Items Kerberoasting Process Discovery Shared Webroot Screen Capture Multi-Stage Channels Service Stop Local Job Scheduling Component Object Model Hijacking Image File Execution Options Injection DCShadow Keychain Query Registry SSH Hijacking Video Capture Multiband Communication Stored Data Manipulation LSASS Driver Create Account Launch Daemon Deobfuscate/Decode Files or Information LLMNR/NBT-NS Poisoning and Relay Remote System Discovery Taint Shared Content Multilayer Encryption Transmitted Data Manipulation Mshta DLL Search Order Hijacking New Service Disabling Security Tools Network Sniffing Security Software Discovery Third-party Software Port Knocking PowerShell Dylib Hijacking Path Interception DLL Search Order Hijacking Password Filter DLL System Information Discovery Windows Admin Shares Remote Access Tools Regsvcs/Regasm External Remote Services Plist Modification DLL Side-Loading Private Keys System Network Configuration Discovery Windows Remote Management Remote File Copy Regsvr32 File System Permissions Weakness Port Monitors Execution Guardrails Securityd Memory System Network Connections Discovery Standard Application Layer Protocol Rundll32 Hidden Files and Directories Process Injection Exploitation for Defense Evasion Two-Factor Authentication Interception System Owner/User Discovery Standard Cryptographic Protocol Scheduled Task Hooking Scheduled Task Extra Window Memory Injection System Service Discovery Standard Non-Application Layer Protocol Scripting Hypervisor Service Registry Permissions Weakness File Deletion System Time Discovery Uncommonly Used Port Service Execution Image File Execution Options Injection Setuid and Setgid File Permissions Modification Virtualization/Sandbox Evasion Web Service Signed Binary Proxy Execution Kernel Modules and Extensions SID-History Injection File System Logical Offsets
Источник: [https://torrent-igruha.org/3551-portal.html]
,
IObit Uninstaller 8.6.0.6 Archives Iobit Uninstaller Pro 8.6.0.6 Amount Lifetime Cleft (Never Expire) (Aio)
IObit Uninstaller 8 is a tool that helps yous to take away unwanted programs too folders from your figurer fast too easily. It allows yous to take away installed applications from your computer, along amongst their leftovers.
IObit Uninstaller 8 tin notice too categorize all of the installed programs. H5N1 listing of installed programs is automatically displayed upon initialization, inward which yous tin persuasion the name, size too install appointment of each software. Moreover, it allows volume uninstallation amongst simply ONE click!
With “Powerful Scan” too “Forced Uninstall” features, you’ll never hold out bothered past times leftovers or stubborn toolbars anymore.
- INFO / DOWNLOAD
- SYSTEM REQUIREMENTS
- HOW TO INSTALL
- SCREENSHOTS
Lighter & Cleaner PC
- Need to uninstall programs too gratis upwards disk space? IObit Uninstaller 8 is the i yous tin trust, whether programs no longer beingness used, can’t beingness uninstalled through measure uninstallation or bundled amongst other programs. It also introduces an tardily agency to uninstall programs. You tin rapidly take away programs via desk icon, opened window or organisation tray icon.
Safer & Faster Browsing
- Once malicious toolbar teach to your figurer they mightiness conduct hold over your browsers past times changing settings without permission. What’s worse, yous would halt upwards inward privacy leaking too dull internet. IObit Uninstaller 8 Free lists all toolbars too marks out the malicious ones installed on main-stream browsers: Chrome, Firefox, IE, Opera, allowing yous to bring out too delete them quickly.
No Leftover Files
- Regular uninstallation cannot delete programs completely. With IObit Uninstaller 8, yous don’t involve to worry close leftovers whatever more. IObit Uninstaller 8 removes leftovers automatically afterward uninstalling programs. Even those leftover files cannot hold out deleted past times other uninstallers; yous tin yet count on it.
Update Software Simply
- Outdated software is risky. Attackers tin easily bring out weakness inward it resulting whole organisation hold out inward danger. IObit Uninstaller 8 Free is at that spot keeping over lx critical programs upwards to appointment for you. You tin easily update software via secure download links to the latest version on publishers’ websites.
Features
- Promptly & Thoroughly Uninstall
- Powerful Remove Plug-ins & Toolbar
- Filtered Choices for Software Uninstalling
- One-Stop Solution to Stubborn Programs Uninstall
- Windows Software Management
- Easy-to-Use PC Toolkit
- System Security Protection
- One-Click Removal of Software Leftovers
- Increased Database for Better PC Protection & Deeper Cleaning
Changes inward IObit Uninstaller 8.6.0.6 :
- Improved the algorithm to also recognize Windows apps: WinZip Microsoft Store Edition, Telegram Desktop, etc.
- Enhanced Software Updater to update software to a greater extent than timely too accurately.
- Optimized Bundleware to scope wrong detection for around programs.
- Fixed known bugs.
DOWNLOAD(26.8 MB)
DOWNLOAD(26.8 MB)
System Requirements
- Microsoft® Windows® XP, Windows® Vista, Windows® seven (SP1), Windows® 8, Windows® 8.1 & Windows® 10 (32-bit, 64-bit All Editions)
- 300 MB Disk Spac
- 1024x768 Screen Resolution too Above
How to Install
- Unpack too Run Software
- Choose Setup too Install
- After Install Don’t Launch or Run Application
- Choose Crack too Click Install to the Directory
- That’s All, Enjoy
Share This :
Источник: [https://torrent-igruha.org/3551-portal.html]
Tag Archives: IObit Uninstaller Pro 8.6.0.6 patch
IObit Uninstaller 9.2.0.20 Crack & Activation Code Full Free Download IObit Uninstaller 9.2.0.20 Crack With Key is an uninstaller for the batch program that cleans all the left log and unwanted file that can take away all the following knowledge from the browser and detect auto-package third-party removal activity. What’s more, if you want to… Read More »
Category: SoftwaresTags: IObit Uninstaller Pro 8.6.0.6 activation code, IObit Uninstaller Pro 8.6.0.6 crack, IObit Uninstaller Pro 8.6.0.6 free download, IObit Uninstaller Pro 8.6.0.6 key, IObit Uninstaller Pro 8.6.0.6 keygen, IObit Uninstaller Pro 8.6.0.6 license key, IObit Uninstaller Pro 8.6.0.6 patch, IObit Uninstaller Pro 8.6.0.6 registration code, IObit Uninstaller Pro 8.6.0.6 serial key, IObit Uninstaller Pro 8.6.0.6 serial number, IObit Uninstaller Pro 9.2.0.16 CrackИсточник: [https://torrent-igruha.org/3551-portal.html]
.
What’s New in the IObit Uninstaller 8.6.0.6 Archives?
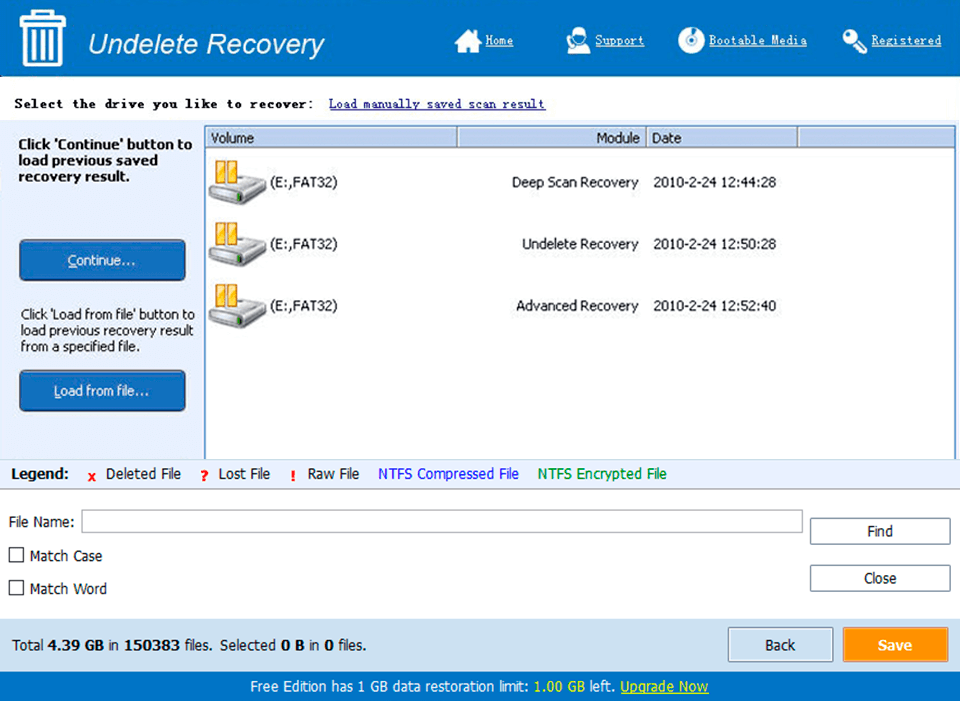
Screen Shot
System Requirements for IObit Uninstaller 8.6.0.6 Archives