Install TweakBox on PC Archives

Install TweakBox on PC Archives
garden shed plans ireland
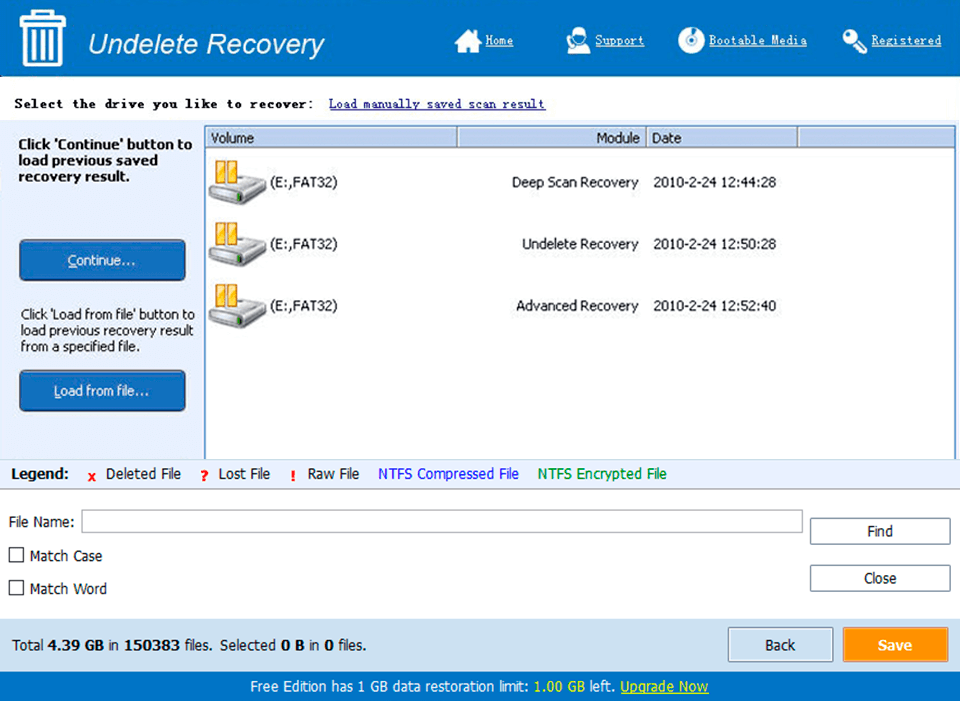
Tweakbox is a mobile app installer that can be downloaded on an iphone, ipad, or apple device. by installing tweakbox, users will have access to applications not available within a device’s respective app store.. Tweakbox offers many different apps and games, all placed into categories so you can search much easier app store apps – ios app store apps, games for free exclusive apps – best emulators, movie apps, screen recorders, and more besides.. Tweakbox app is a popular app store, which is used to download third-party apps. when you notice that you can’t find certain applications of google play store, you need to look for an alternate. this is the point where you need to look at nowhere else but tweakbox ..

If you are impressed with the feature of the app, then proceed to the next section to know how to download and install the app on your device. how to download and install tweakbox on your device? tweakbox is not available in google play store. and therefore, the only way to install the app on your device is through the apk file of the app.. Tweakbox apps – the cydia apps – emulators, screen recorders like airshou, music and movie apps and so much more how to download tweakbox : tweakbox is very easy to install but don’t waste your time looking for it in the app store.. Install jailbreak apps & plus plus apps free without jailbreaking cydia alternative ios 9.3.4, 9.3.5, ios 10.2 tweakbox app: http://tweakboxapp.com.
iOS jailbreaking
Jailbreaking is the privilege escalation of an Apple device for the purpose of removing software restrictions imposed by Apple on iOS, iPadOS, tvOS, watchOS, and bridgeOS operating systems. This is typically done by using a series of kernelpatches. Jailbreaking permits root access in Apple's mobile operating system, allowing the installation of software that is unavailable through the official Apple App Store. Many types of jailbreaking are available, for different versions. Because Apple publicly disapproves of jailbreaking,[1] Apple has implemented hardware and software fixes to the vulnerabilities used in jailbreaks, meaning that many versions of iOS are not jailbroken immediately. It is analogous to rooting on Android, although software unavailable on Google Play can be installed on Android without rooting; in recent years the unauthorised use of enterprise certificates has led to the emergence of alternative app stores for iOS allowing for the installation of modified or pirated apps without jailbreaking. There are four types of jailbreaks today. These include: Tethered jailbreaks, untethered jaibreaks, semi-tethered jailbreaks, and semi-untethered jailbreaks.
Motivations[edit]
One of the reasons for jailbreaking is to expand the feature set limited by Apple and its App Store.[2] Apple checks apps for compliance with its iOS Developer Program License Agreement before accepting them for distribution in the App Store. However, their reasons for banning apps are not limited to safety and security and may be regarded as arbitrary and capricious.[3] In one case, Apple mistakenly banned an app by a Pulitzer-Winning cartoonist because it violated its developer license agreement, which specifically bans apps that "contain content that ridicules public figures."[4] To access banned apps,[5] users rely on jailbreaking to circumvent Apple's censorship of content and features. Jailbreaking permits the downloading of programs not approved by Apple,[6] such as user interface customization and tweaks.
Device customization[edit]
Since software programs available through APT and or Installer.app (legacy) are not required to adhere to App Store guidelines, many of them are not typical self-contained apps but instead are extensions and customization options for iOS and its features and other apps (commonly called tweaks).[7] Users install these programs for purposes including personalization and customization of the interface by tweaks developed by developers and designers,[7] adding desired features such as access to the root file system and fixing annoyances,[8] and making development work on the device easier by providing access to the filesystem and command-line tools.[9][10] Many Chinese iOS device owners also jailbreak their phones to install third-party Chinese character input systems because they are easier to use than Apple's.[11]
Carrier unlocking[edit]
Jailbreaking also opens the possibility for using software to unofficially unlock carrier-locked iPhones so they can be used with other carriers.[12] Software-based unlocks have been available since September 2007,[13] with each tool applying to a specific iPhone model and baseband version (or multiple models and versions).[14] This includes the iPhone 4S, iPhone 4, iPhone 3GS, and iPhone 3G models. An example of unlocking an iPhone through a Jailbreak utility would be Redsn0w. Through this software, iPhone users will be able to create a custom IPSW and unlock their device. Moreover, during the unlocking process, there are options to install Cydia the iPad baseband.
Installation of malware[edit]
Computer criminals may jailbreak an iPhone to install malware or target jailbroken iPhones on which malware can be installed more easily. The Italian cybersecurity company Hacking Team, which sells hacking software to law enforcement agencies, advised police to jailbreak iPhones to allow tracking software to be installed on them.[15][16]
Software piracy[edit]
On iPhones, the installation of consumer software is generally restricted to installation through the App Store. Jailbreaking, therefore, allows the installation of pirated applications.[17] It has been suggested that a major motivation for Apple to prevent jailbreaking is to protect the income of its App Store, including third-party developers and allow the buildup of a sustainable market for third-party software.[18] However, the installation of pirated applications is also possible without jailbreaking, taking advantage of enterprise certificates to facilitate distribution of modified or pirated releases of popular applications.[19]
Types of jailbreaks[edit]

When a jailbroken device is booting, it loads Apple's own kernel initially. The device is then exploited and the kernel is patched every time it is turned on. Many different types of jailbreaks have come out over the years. An untethered jailbreak is a jailbreak that does not require any assistance when it reboots up. The kernel will be patched without the help of a computer or an application.[20] These jailbreaks are uncommon and take a significant amount of reverse engineering to create. A tethered jailbreak is the opposite of an untethered jailbreak, in the sense that a computer is required to boot, and the device will not boot by itself. While using a tethered jailbreak, the user will still be able to restart/kill the springboard without needing to reboot. A mix between an untethered and a tethered jailbreak is also an option, namely semi-tethered. This type of jailbreak allows the user to reboot, but there will not be a patched kernel. Non-jailbroken functions will still run, such as making a phone call, texting, or using an app. To be able to have a patched kernel and run modified code again, the device must be booted using a computer. A type of jailbreak that has become popular in the recent years, is the semi-untethered variant. This type of jailbreak is like a semi-tethered jailbreak in which when the device reboots, it no longer has a patched kernel, but the kernel can be patched without using a computer. The kernel is usually patched using an application installed on the device. Most recent jailbreaks have been the semi-untethered variant.
Comparison to Android rooting[edit]
Jailbreaking of iOS devices has sometimes been compared to "rooting" of Android devices. Although both concepts involve privilege escalation, they do differ in scope.
Where Android rooting and Jailbreaking are similar is that both are used to grant the owner of the device superuser system-level privileges, which may be transferred to one or more apps. However, unlike iOS phones and tablets, nearly all Android devices already offer an option to allow the user to sideload 3rd-party apps onto the device without having to install from an official source such as the Google Play store.[21] Many Android devices also provide owners the capability to modify or even replace the full operating system after unlocking the bootloader.[22][23][24]
In contrast, iOS devices are engineered with security features including a "locked bootloader" which can not be unlocked by the owner to modify the operating system without violating Apple's end-user license agreement. And on iOS, until 2015, while corporations could install private applications onto corporate phones, sideloading unsanctioned, 3rd-party apps onto iOS devices from sources other than the Apple Store was prohibited for most individual users without a purchased developer membership.[25] After 2015, the ability to install 3rd-party apps became free for all users; however, doing so requires a basic understanding of Xcode and compiling iOS apps.
Jailbreaking an iOS device to defeat all these security restrictions presents a significant technical challenge.[26] Similar to Android, alternative iOS app stores utilizing enterprise certificates are available, offering modified or pirated releases of popular applications and video games, some of which were either previously released through Cydia or are unavailable on the App Store due to these apps not complying with Apple developer guidelines.
Security, privacy and stability[edit]
The first iPhoneworm, iKee, appeared in early November 2009, created by a 21-year-old Australian student in the town of Wollongong. He told Australian media that he created the worm to raise awareness of security issues: jailbreaking allows users to install an SSH service, which those users can leave in the default insecure state.[27] In the same month, F-Secure reported on a new malicious worm compromising bank transactions from jailbroken phones in the Netherlands, similarly affecting devices where the owner had installed SSH without changing the default password.[28][29]
In 2010 blogger John Gruber, who is close to Apple, said that users misunderstood some jailbreak exploits and that they were more serious than they appear. He commented that "it's odd how the press is mostly covering this as 'jailbreaking now more convenient' rather than 'remote code exploit now in the wild'", pointing out that the exploit allowed the creator of a malicious website to take control of iPhones accessing it.[30] Restoring a device with iTunes removes a jailbreak.[31][32][33] However, doing so generally updates the device to the latest, and possibly non-jailbreakable, version, due to Apple's use of SHSH blobs. There are many applications that aim to prevent this, by restoring the devices to the same version they are currently running whilst removing the jailbreaks. Examples are, Succession, Semi-Restore and Cydia Eraser.
In 2012, Forbes staff analyzed a UCSB study on 1,407 free programs available from Apple and a third party source. Of the 1,407 free apps investigated, 825 were downloaded from Apple's App Store using the website App Tracker, and 526 from BigBoss (Cydia's default repository). 21% of official apps tested leaked device ID and 4% leaked location. Unofficial apps leaked 4% and 0.2% respectively. 0.2% of apps from Cydia leaked photos and browsing history, while the App Store leaked none. Unauthorized apps tended to respect privacy better than official ones.[34] Also, a program available in Cydia called PrivaCy allows user to control the upload of usage statistics to remote servers.[34]
In August 2015 the KeyRaider malware was discovered that affects only jailbroken iPhones.[35]
History of exploit-disabling patch releases[edit]
Apple has released various updates to iOS that patch exploits used by jailbreak utilities; this includes a patch released in iOS 6.1.3 to software exploits used by the original evasi0n iOS 6–6.1.2 jailbreak, in iOS 7.1 patching the Evasi0n 7 jailbreak for iOS 7–7.0.6-7.1 beta 3. Bootroom exploits (exploits found in the hardware of the device) cannot be patched by Apple system updates, but can be fixed in hardware revisions such as new chips or new hardware in its entirety, as occurred with the iPhone 3GS in 2009.[36]
On July 15, 2011, Apple released a new iOS version that closed the exploit used in JailbreakMe 3.0. The German Federal Office for Information Security had reported that JailbreakMe uncovered the "critical weakness" that information could be stolen or malware unwillingly downloaded by iOS users clicking on maliciously crafted PDF files.[37] Before Apple released a fix for this security hole, jailbreak users had access to a fix published by the developer of JailbreakMe.[citation needed]
On January 27, 2015, Apple released iOS 8.1.3 that patched up the exploits used in jailbreak for iOS 8.0–8.1.2. It was not possible to jailbreak until the iOS 8.3 update.
On August 13, 2015, Apple updated iOS to 8.4.1, patching the TaiG exploit. Pangu and Taig teams both said they were working on exploiting iOS 8.4.1, and Pangu demonstrated these chances at the WWDC 2015.[38]
On September 16, 2015, iOS 9 was announced and made available; it was released with a new "Rootless" security system, dubbed a "heavy blow" to the jailbreaking community.[39]
On October 21, 2015, seven days after the Pangu iOS 9.0–9.0.2 Jailbreak release, Apple pushed the iOS 9.1 update, which contained a patch that rendered it nonfunctional.[40]
On August 4, 2016, Apple released iOS version 9.3.4 to patch the semi-untethered jailbreak for 64-bit devices.
On August 25, 2016, Apple released iOS version 9.3.5 to patch three important vulnerabilities used for the secret jailbreak from the Pegasus Malware from the NSO Group.
On January 23, 2017, Apple released iOS 10.2.1 to patch jailbreak exploits released by Google for the Yalu iOS 10 jailbreak created by Luca Todesco.[41]
On December 2, 2017, iOS 11.2 was released, and included a patch to the async_wake exploit by Ian Beer of Google Project Zero.
On May 29, 2018, iOS 11.4 was released, including a patch to 2 exploits (empty_list and multi_path) by Ian Beer of Google Project Zero.
On January 22, 2019, iOS 12.1.3 was released, including a patch to an exploit (voucher_swap), found independently by both Brandon Azad of Google Project Zero, and Zhuo Liang of Qihoo 360 Nirvan Team.
On May 13, 2019, iOS 12.3 was released, including a patch to an exploit (sock_puppet) by Ned Williamson of Google Project Zero. However, on the 18th of August 2019, it became known that Apple accidentally reintroduced these vulnerabilities in iOS 12.4, making it possible to jailbreak 12.4 with the same exploits as pre-12.3 versions.
On August 26, 2019, Apple released the 12.4.1 update, re-patching the exploit (sock_puppet) by Ned Williamson of Google Project Zero.
On November 10, 2019, a group of developers released a jailbreak named "Checkra1n", which exploits the chips found in devices ranging from A5-A11 devices. This was the first jailbreak to feature a bootrom exploit in a decade. The tool utilizes the "Checkm8" exploit developed by Axi0mX.
On December 10, 2019, Apple used DMCA takedown requests to remove posts from Twitter. The tweet contained an encryption key that could potentially be used to reverse engineer the iPhone's Secure Enclave. Apple later retracted the claim, and the tweet was reinstated.[42]
On June 1, 2020 Apple released the 13.5.1 update, patching the 0 day exploit used by the Unc0ver jailbreak.[43]
Legality[edit]
The legal status of jailbreaking is affected by laws regarding circumvention of digital locks, such as laws protecting digital rights management (DRM) mechanisms. Many countries do not have such laws, and some countries have laws including exceptions for jailbreaking.
International treaties have influenced the development of laws affecting jailbreaking. The 1996 World Intellectual Property Organization (WIPO) Copyright Treaty requires nations party to the treaties to enact laws against DRM circumvention. The American implementation is the Digital Millennium Copyright Act (DMCA), which includes a process for establishing exemptions for non-copyright-infringing purposes such as jailbreaking. The 2001 European Copyright Directive implemented the treaty in Europe, requiring member states of the European Union to implement legal protections for technological protection measures. The Copyright Directive includes exceptions to allow breaking those measures for non-copyright-infringing purposes, such as jailbreaking to run alternative software,[44] but member states vary on the implementation of the directive.
While Apple technically does not support jailbreaking as a violation of its EULA, jailbreaking communities have generally not been legally threatened by Apple. At least two prominent jailbreakers have been given positions at Apple, albeit in at least one case a temporary one.[45][46] Apple has also regularly (though possibly somewhat jokingly) thanked jailbreak communities for detecting security holes in iOS release notes.[47]
Apple's support article concerning jailbreaking claims that they "may deny service for an iPhone, iPad, or iPod touch that has installed any unauthorized software."[48] Therefore, anyone who is jailbroken, warranty or not, may or may not get support from Apple considering assistance with jailbreaking.
Australia[edit]
In 2010, Electronic Frontiers Australia said that it is unclear whether jailbreaking is legal in Australia, and that anti-circumvention laws may apply.[49] These laws had been strengthened by the Copyright Amendment Act 2006.
Canada[edit]
In November 2012, Canada amended its Copyright Act with new provisions prohibiting tampering with DRM protection, with exceptions including software interoperability.[50] Jailbreaking a device to run alternative software is a form of circumventing digital locks for the purpose of software interoperability.
There had been several efforts from 2008–2011 to amend the Copyright Act (Bill C-60, Bill C-61, and Bill C-32) to prohibit tampering with digital locks, along with initial proposals for C-11 that were more restrictive,[51] but those bills were set aside. In 2011, Michael Geist, a Canadian copyright scholar, cited iPhone jailbreaking as a non-copyright-related activity that overly-broad Copyright Act amendments could prohibit.[52]
India[edit]
India's copyright law permits circumventing DRM for non-copyright-infringing purposes.[53][54] Parliament introduced a bill including this DRM provision in 2010 and passed it in 2012 as Copyright (Amendment) Bill 2012.[55] India is not a signatory to the WIPO Copyright Treaty that requires laws against DRM circumvention, but being listed on the US Special 301 Report "Priority Watch List" applied pressure to develop stricter copyright laws in line with the WIPO treaty.[53][54]
New Zealand[edit]
New Zealand's copyright law allows the use of technological protection measure (TPM) circumvention methods as long as the use is for legal, non-copyright-infringing purposes.[56][57] This law was added to the Copyright Act 1994 as part of the Copyright (New Technologies) Amendment Act 2008.
Singapore[edit]
Jailbreaking might be legal in Singapore if done to provide interoperability and not circumvent copyright, but that has not been tested in court.[58]
United Kingdom[edit]
The law Copyright and Related Rights Regulations 2003 makes circumventing DRM protection measures legal for the purpose of interoperability but not copyright infringement. Jailbreaking may be a form of circumvention covered by that law, but this has not been tested in court.[44][59] Competition laws may also be relevant.[60]
United States[edit]
The main law that affects the legality of iOS jailbreaking in the United States is the 1998 Digital Millennium Copyright Act (DMCA), which says "no person shall circumvent a technological measure that effectively controls access to a work protected under" the DMCA, since this may apply to jailbreaking.[61] Every three years, the law allows the public to propose exemptions for legitimate reasons for circumvention, which last three years if approved. In 2010 and 2012, the U.S. Copyright Office approved exemptions that allowed smartphone users to jailbreak their devices legally,[62] and in 2015 the Copyright Office approved an expanded exemption that also covers other all-purpose mobile computing devices, such as tablets.[63] It is still possible Apple may employ technical countermeasures to prevent jailbreaking or prevent jailbroken phones from functioning.[64] It is unclear whether it is legal to traffic in the tools used to make jailbreaking easy.[64]
In 2010, Apple announced that jailbreaking "can violate the warranty".[65] This may be affected by the Magnuson–Moss Warranty Act.
Digital Millennium Copyright Act exemptions[edit]
In 2007, Tim Wu, a professor at Columbia Law School, argued that jailbreaking "Apple's superphone is legal, ethical, and just plain fun."[66] Wu cited an explicit exemption issued by the Library of Congress in 2006 for personal carrier unlocking, which notes that locks "are used by wireless carriers to limit the ability of subscribers to switch to other carriers, a business decision that has nothing whatsoever to do with the interests protected by copyright" and thus do not implicate the DMCA.[67] Wu did not claim that this exemption applies to those who help others unlock a device or "traffic" in software to do so.[66]
In 2010, in response to a request by the Electronic Frontier Foundation, the U.S. Copyright Office explicitly recognized an exemption to the DMCA to permit jailbreaking in order to allow iPhone owners to use their phones with applications that are not available from Apple's store, and to unlock their iPhones for use with unapproved carriers.[68][69]Apple had previously filed comments opposing this exemption and indicated that it had considered jailbreaking to be a violation of copyright (and by implication prosecutable under the DMCA). Apple's request to define copyright law to include jailbreaking as a violation was denied as part of the 2009 DMCA rulemaking. In their ruling, the Library of Congress affirmed on July 26, 2010 that jailbreaking is exempt from DMCA rules with respect to circumventing digital locks. DMCA exemptions must be reviewed and renewed every three years or else they expire.
On October 28, 2012, the US Copyright Office released a new exemption ruling. The jailbreaking of smartphones continued to be legal "where circumvention is accomplished for the sole purpose of enabling interoperability of [lawfully obtained software] applications with computer programs on the telephone handset." However, the U.S. Copyright office refused to extend this exemption to tablets, such as iPads, arguing that the term "tablets" is broad and ill-defined, and an exemption to this class of devices could have unintended side effects.[70][71][72] The Copyright Office also renewed the 2010 exemption for unofficially unlocking phones to use them on unapproved carriers, but restricted this exemption to phones purchased before January 26, 2013.[71] In 2015, these exemptions were extended to include other devices, including tablets.[73]
History of tools[edit]

A few days after the original iPhone became available in July 2007, developers released the first jailbreaking tool for it,[74] and soon a jailbreak-only game app became available.[75] In October 2007, JailbreakMe 1.0 (also called "AppSnapp") allowed people to jailbreak iPhone OS 1.1.1 on both the iPhone and iPod touch,[76][77] and it included Installer.app as a way to get software for the jailbroken device. In February 2008, Zibri released ZiPhone, a tool for jailbreaking iPhone OS 1.1.3 and iPhone OS 1.1.4.[78]
The iPhone Dev Team, which is not affiliated with Apple, has released a series of free desktop-based jailbreaking tools. In July 2008 it released a version of PwnageTool to jailbreak the then new iPhone 3G on iPhone OS 2.0 as well as the iPod touch,[79][80] newly including Cydia as the primary third-party installer for jailbroken software.[81] PwnageTool continues to be updated for untethered jailbreaks of newer iOS versions.[82][83]
In November 2008 the iPhone Dev Team released QuickPwn to jailbreak iPhone OS 2.2 on iPhone and iPod touch, with options to enable past functionality that Apple had disabled on certain devices.[84]
After Apple released iOS 3.0 in June 2009, the Dev Team published redsn0w as a simple jailbreaking tool for Mac and Windows, and also updated PwnageTool primarily intended for expert users making custom firmware, and only for Mac.[85] It continues to maintain redsn0w for jailbreaking most versions of iOS 4 and iOS 5 on most devices.[86]
George Hotz developed the first iPhone unlock. In 2009, he released a jailbreaking tool for the iPhone 3GS on iPhone OS 3.0 called purplera1n,[87] and blackra1n for iPhone OS version 3.1.2 on the 3rd generation iPod touch and other devices.[88]
In October 2010, he released limera1n, a low-level boot ROM exploit that permanently works to jailbreak the iPhone 4 and is used as a part of tools including redsn0w.[89]
Nicholas Allegra (better known as "comex") released a program called Spirit in May 2010.[citation needed] Spirit jailbreaks devices including iPhones running iPhone OS 3.1.2, 3.1.3, and iPad running iOS 3.2.[90] In August 2010, comex released JailbreakMe 2.0, the first web-based tool to jailbreak the iPhone 4 (on iOS 4.0.1).[91][92] In July 2011, he released JailbreakMe 3.0,[93] a web-based tool for jailbreaking all devices on certain versions of iOS 4.3, including the iPad 2 for the first time (on iOS 4.3.3).[94] It used a flaw in PDF file rendering in mobile Safari.[95][96]
Chronic Dev Team initially released Greenpois0n in October 2010, a desktop-based tool for jailbreaking iOS 4.1[97] and later iOS 4.2.1[98] on most devices including the Apple TV,[99] as well as iOS 4.2.6 on CDMA (Verizon) iPhones.[100]
As of December 2011, redsn0w included the "Corona" untether by pod2g for iOS 5.0.1 for iPhone 3GS, iPhone 4, iPad (1st generation), and iPod touch (3rd and 4th generation).[83] As of June 2012, redsn0w also includes the "Rocky Racoon" untether by pod2g for iOS 5.1.1 on all iPhone, iPad, and iPod touch models that support iOS 5.1.1.[101]
The iPhone Dev Team, Chronic Dev Team, and pod2g collaborated to release Absinthe in January 2012, a desktop-based tool to jailbreak the iPhone 4S for the first time and the iPad 2 for the second time, on iOS 5.0.1 for both devices and also iOS 5.0 for iPhone 4S.[20][102][103][104] In May 2012 it released Absinthe 2.0, which can jailbreak iOS 5.1.1 untethered on all iPhone, iPad, and iPod touch models that support iOS 5.1.1, including jailbreaking the third-generation iPad for the first time.[105] The hackers together called the evad3rs released an iOS 6.X jailbreak tool called "evasi0n" available for Linux, OS X, and Windows on Monday, February 4, 2013 at noon Eastern Standard Time.[citation needed] Due to the high volume of interest in downloading the jailbreak utility, the site initially gave anticipating users download errors.[citation needed] When Apple upgraded its software to iOS 6.1.3 it permanently patched out the evasi0n jailbreak.[106] In April 2013, the latest versions of Sn0wbreeze was released, which added the support for tethered jailbreaking on A4 devices (i.e. devices not newer than the iPhone 4, iPad (1st generation), or iPod touch (4th generation)).[107][108][109]
On December 22, 2013, the evad3rs released a new version of evasi0n that supports jailbreaking iOS 7.0.x, known as evasi0n7.[citation needed] On December 30, 2013, winocm, ih8sn0w and SquiffyPwn released p0sixspwn for untethering devices on iOS 6.1.3 – 6.1.5. Initially, it was necessary to jailbreak tethered using redsn0w and install p0sixpwn at Cydia. A few days later, on January 4, 2014, the same team released a version of p0sixpwn for jailbreaking using a computer.[citation needed]
iOS 7.1 patched the exploits used by evasi0n7, and on June 23, 2014, Pangu, a Chinese untethered jailbreak was released for iOS 7.1.[citation needed]
On October 22, 2014, Pangu Team released Pangu8 to jailbreak all devices running iOS 8–8.1. The first versions did not bundle Cydia, nor was there an iOS 8 compatible version of Cydia at the time.[citation needed]
On November 29, 2014, TaiG team released their jailbreak tool called "TaiG" for devices running iOS 8.0–8.1.1. On December 10, 2014, the app was updated to include support for iOS 8.1.2.[110] On July 3, 2015, TaiG 2.3.0 was released, which includes support for iOS 8.0–8.4.[111]
On 10 September 2015, 6 days before iOS 9 was released, iH8sn0w had demonstrated a working exploit on his Twitter page, linking to a YouTube video.[112]
On October 14, 2015, Pangu Team released Pangu9, their jailbreak tool for iOS 9.0 through 9.0.2. On March 11, 2016, Pangu Team updated their tool to support iOS 9.1 for 64-bit devices.[113][114][115]
On July 17, 2016, Pangu Team released Pangu93, a semi-untethered jailbreak tool for iOS 9.2–9.3.3. It was the first semi-untethered jailbreak and at the same time made within a sideloaded app, and included support only for 64bit devices.[116]
On mid-March 2017, jk9357 (aka @REALKJCMEMBER), part of the KJC (Kim Jong Cracks) hacking team released the first semi-untethered jailbreak for 32bit devices on 9.1–9.3.4. This jailbreak made use of some of the Pegasus vulnerabilities.[117]
On December 21, 2016, well-known hacker Luca Todesco released a beta semi-untethered jailbreak tool for iOS 10.1 known as yalu+mach_portal for select 64-bit iOS devices. The jailbreak made use of Ian Beer's, of Google Project Zero, mach_portal exploit. This version is extremely unstable and was only meant for developers.[118] On January 26, 2017, he with help from Marco Grassi, a more stable version for iOS 10.2 was released, eventually supporting all 64-bit iOS devices except for the iPhone 7 and 7 Plus, which is only supported by the older, more unstable version for 10.1.1. This jailbreak made use of Ian Beer's, of Project Zero, extra_recipe exploit. Both jailbreaks are installed through a computer application known as Cydia Impactor, which allows signing of apps not in the App Store.[119] Todesco said that the newer version would be eventually updated to support the iPhone 7 and 7 Plus up to iOS 10.1.1, however, he left the jailbreaking scene on March 28, abandoning both jailbreaks before it was released.
On August 6, 2017, Siguza and tihmstar released the semi-untethered Phoenix jailbreak for 32-bit devices on iOS 9.3.5.
On September 19, 2017, tihmstar released EtasonJB, a jailbreak for all 32-bit devices on iOS 8.4.1. An exploit was found so that users of the 9.3.5 Phoenix jailbreak could downgrade to 8.4.1 without the use of SHSH blobs as 8.4.1 is an unsigned version of iOS.
On October 15, 2017, the hacker Abraham Masri (known on Twitter as @cheesecakeufo) released the Saïgon jailbreak for all 64-bit devices on iOS 10.2.1.
On December 6, 2017, Abraham Masri released Houdini, the first semi-jailbreak for iOS 10, compatible with iOS 10.x up to 10.3.2 for all 64-bit devices. The application allows installation of themes, resolution changes etc. from basic Cydia repos. It is untethered, but it needs to run the exploit again to install content. The tool has been updated to beta revision 1, adding the compatibility with iOS 11 up to 11.1.2.
On December 11, 2017, Ian Beer released async_wake, an iOS 11.0 up to 11.1.2 exploit that allows tfp0. The exploit has been updated and it has allowed jailbreak apps on jailed devices such as FilzaJailed, FilzaEscaped (which allows root access on a jailed device), MTerminal-Jailed by Ayden Panhuyzen (which allows the execution of commands on a jailed device) and Torngat by 1GamerDev (a tweak manager that can set a boot logo, change resolution, disable OTA updates and more on a jailed device).
On December 23, 2017, Abraham Masri released to.panga, an iOS 11 up to 11.1.2 WIP jailbreak for developers based on the async_wake exploit by Ian Beer. It has Cydia included but since the jailbreak used a KPPless exploit, Cydia and Substrate have to be rewritten. Abraham Masri has since stated that the project wouldn't be updated due to other tools with the same goal.
On December 24, 2017, tihmstar released h3lix, a semi-untethered jailbreak for all 32-bit devices, compatible with all iOS 10 versions.
Shortly after the release of h3lix, tihmstar and Siguza released doubleH3lix, a semi-untethered jailbreak for 64bit devices (excluding the iPhone 7) on iOS 10.x.
On December 26, 2017 the hacker Jonathan Levin (known on Twitter as @Morpheus____) released LiberiOS, a WIP developer-only jailbreak based on the async_wake exploit by Ian Beer for iOS 11.0 to iOS 11.1.2. Jonathan Levin later stated that LiberiOS would not be officially released with Cydia.
On January 29, 2018, Zimperium, whose goal is to assess issues and locate a possible iOS sandbox escape, released two crucial bugs, one of which is a major vulnerability that leads to execution of arbitrary code on different crucial daemons, found in iOS 11.2 up to 11.2.2. The second bug is a full relative (ASLR bypass) control on the stack in CoreBluetooth, that leads to memory corruption (also on 11.2 – 11.2.2).
On February 26, 2018, developer CoolStar (known on Twitter as @CStar_OW)[120] released a public version of the Electra jailbreak for iOS devices on 11.0–11.1.2.[121] This jailbreak uses a KPPless exploit. As Cydia Substrate had not been updated for iOS 11, Electra uses a Substrate alternative known as Substitute.
On June 6, 2018, Abraham Masri released an update to Houdini, the first semi-jailbreak. The tool has been updated to beta 3 revision 1, adding the compatibility with iOS 11 up to 11.3.1.[122]
On July 6, 2018, developer CoolStar updated the Electra jailbreak for iOS devices on 11.0–11.3.1 (it previously only supported up to 11.1.2).[121] It continued to use a KPPless exploit and Substitute in place of Cydia Substrate.
On August 17, 2018, developer Ben Sparkes[123] released a public version of Meridian,[124] a jailbreak for iOS versions 10.x on all 64-bit devices.
On September 3, 2018, a web-based jailbreak called "Totally Not Spyware"[125] was released by an unknown user named "JakeBlair420". It eventually came out that it was developed by FoxletFox, Ben Sparkes, littlelailo, siguza, stek29, and was based on the works of 5aelo, Ian Beer, Niklas B, Jamie Bishop, Luca Todesco, REALKJCMEMBER, Sam Bingner, sticktron, theninjaprawn, tihmstar, and xerub. It used a WebKit-based exploit to bootstrap either Meridian or doubleh3lix.
On October 14, 2018, former Electra team member and developer Pwn20wnd (known on Twitter as @Pwn20wnd[126]) released a public version of the unc0ver jailbreak for iOS devices on 11.0–11.4.1.[127] This jailbreak uses the three KPPless exploits provided by Ian Beer for iOS 11 (async_wake, empty_list and multi_path). Pwn20wnd also worked with Jay Freeman, the original developer of Cydia, to get Cydia Substrate reupdated to iOS 11. It was released on December 17, 2018.
On February 22, 2019, developer (Pwn20wnd[126]) released a public update for the unc0ver jailbreak for iOS devices on 12.0–12.1.2.[127] This version of unc0ver uses exploits provided by tihmstar and SorryMyBad for iOS 12 (v1ntex, v3ntex, and voucher_swap). Pwn20wnd once again worked with Jay Freeman to get Cydia and Cydia Substrate updated to work on iOS 12.
On April 29, 2019, the Electra team[128] released Chimera, a public jailbreak for iOS 12.0–12.1.2, which included support for all devices, including devices with A12 chips, which had major security reinforcements compared to other devices. This jailbreak uses Substitute, an alternative to Cydia Substrate, to allow tweaks to run.
On June 12, 2019, developer (Pwn20wnd[129]) released a public update to the unc0ver jailbreak, to add support for iOS 12.1.2–12.2. The jailbreak did not support A8 and A7 devices to begin with, but support for those devices has now been added for iOS 12.1.2–12.2.
On August 18, 2019, developer (Pwn20wnd[129]) released a public update to the unc0ver jailbreak, to add support for iOS 12.4 following a mistake by Apple that reintroduced the vulnerabilities patched in 12.3. This version of unc0ver used the sock_puppet exploit, developed by Ned Williamson and the sock_port exploit, developed by Jake James.
On September 27, 2019, security researcher (axi0mX[130]) released an exploit for some iPhone bootroms dubbed checkm8 (read as checkmate), that executes when the device is started up, and cannot be patched by Apple. This exploit affects A5-A11 (iPhone 4s–iPhone X) devices, and due to the nature of the exploit it supports any iOS version running on these supported devices. According to the developer, an exploit this powerful has not been released since 2010. Although checkm8 is purely an exploit tool, and not a jailbreak tool, a semi-tethered jailbreak has been achieved as of September 27, 2019, and a beta version of checkra1n, a jailbreak tool that uses checkm8 has been released for macOS and Linux, with a windows version in the works.
On December 9, 2019, developer (Pwn20wnd[129]) released a public update to the unc0ver jailbreak, to add support for iOS 12.4.1.[131] This version of unc0ver used the AppleAVE2Driver exploit,[132] developed by 08Tc3wBB, who submitted/sold the exploit to ZecOps for the Task-For-Pwn 0 Bounty.
On January 22, 2020, tihmstar released EtasonATV, a jailbreak for Apple TV (3rd generation Rev A) on iOS 8.4.1–8.4.4.
On January 28, 2020, tihmstar released a public update to the EtasonATV jailbreak, to add support for Apple TV (3rd generation).
On February 15, 2020, developer (Pwn20wnd[129]) released a public update to the unc0ver jailbreak, to add support for iOS 13.0–13.3 for A12 and A13 devices. The jailbreak did not support A11 and below devices to begin with, but has since been updated to do so.
On May 20, 2020, developer (Pwn20wnd[129]) released a public update to the unc0ver jailbreak, to add support for iOS 13.3.1-13.5 for all devices that support that version range.[133]
On June 9, 2020, developer (Pwn20wnd[129]) released a public update to the unc0ver jailbreak, to add support for iOS 13.5.5~b1.[134]
Fake/scam jailbreaks[edit]
Like all popular culture and tech phenomenon, there are people and companies who will attempt to create a profit using less-than ethical means. Although the majority of the time it involves advertising, there are cases involving a scam payment.[135][136] In addition, websites that ask users to either download free-to-play apps or fill out a survey to complete a jailbreak are scams and should be avoided.
By device and OS[edit]
| Device | OS | Release date | Jailbreak date | Jailbroken after (days) | Tool | Developer(s) |
|---|---|---|---|---|---|---|
| iPhone 2G | iPhone OS 1.0 | June 29, 2007 | July 10, 2007[74] | 11 | (no name) | iPhone Dev Team[137] |
| iPod touch | September 5, 2007 | October 10, 2007[138][139] | 35 | (no name) | niacin and dre | |
| iPhone 3G | iPhone OS 2.0 | July 11, 2008 | July 20, 2008[80] | 9 | PwnageTool | iPhone Dev Team |
| iPod touch (2nd generation) | September 9, 2008 | January 30, 2009[140][141] | 143 | redsn0w | iPhone Dev Team and Chronic Dev Team | |
| iPhone OS 3.0 | June 17, 2009 | June 19, 2009[142] | 2 | PwnageTool | iPhone Dev Team | |
| iPhone 3GS | June 19, 2009 | July 3, 2009[143] | 14 | purplera1n | George Hotz | |
| iPad | April 30, 2010 | May 3, 2010[90] | 3 | Spirit | comex | |
| iOS 4.0 | June 21, 2010 | June 23, 2010[144][145] | 2 | PwnageTool | iPhone Dev Team | |
| iPhone 4 | June 24, 2010 | August 1, 2010[91] | 38 | JailbreakMe 2.0 | comex | |
| Apple TV (2nd generation) | September 1, 2010 | October 20, 2010[146] | 49 | PwnageTool | iPhone Dev Team | |
| iPad 2 | March 11, 2011 | July 5, 2011[94] | 116 | JailbreakMe 3.0 | comex | |
| iOS 5.0 | October 12, 2011 | October 13, 2011[86] | 1 | redsn0w | iPhone Dev Team | |
| iPhone 4S | October 14, 2011 | January 20, 2012[20][102] | 98 | Absinthe | pod2g, Chronic Dev Team, iPhone Dev Team | |
| iPad (3rd generation) | March 16, 2012 | May 25, 2012 | 70 | Absinthe 2.0 | pod2g, Chronic Dev Team, iPhone Dev Team | |
| iOS 6.0 | September 19, 2012 | September 19, 2012 | 0 | redsn0w | iPhone Dev Team | |
| iPhone 5 | September 21, 2012 | February 4, 2013 | 136 | evasi0n | evad3rs | |
| iPod touch (5th generation) | October 23, 2012 | February 4, 2013 | 104 | evasi0n | evad3rs | |
| iPad (4th generation) | November 2, 2012 | February 4, 2013 | 94 | evasi0n | evad3rs | |
| iPad Mini | November 2, 2012 | February 4, 2013 | 94 | evasi0n | evad3rs | |
| iOS 7 | September 18, 2013 | December 22, 2013 | 95 | evasi0n7 | evad3rs | |
| iPhone 5C | September 20, 2013 | December 22, 2013 | 93 | evasi0n7 | evad3rs | |
| iPhone 5S | September 20, 2013 | December 22, 2013 | 93 | evasi0n7 | evad3rs | |
| iPad Air | November 1, 2013 | December 22, 2013 | 51 | evasi0n7 | evad3rs | |
| iPad Mini 2 | November 12, 2013 | December 22, 2013 | 40 | evasi0n7 | evad3rs | |
| iOS 8 | September 17, 2014 | October 22, 2014 | 35 | Pangu8 | Pangu Team | |
| iPhone 6 | September 19, 2014 | October 22, 2014 | 33 | Pangu8 | Pangu Team | |
| iPhone 6 Plus | September 19, 2014 | October 22, 2014 | 33 | Pangu8 | Pangu Team | |
| iPad Air 2 | October 22, 2014 | October 22, 2014 | 0 | Pangu8 | Pangu Team | |
| iPad Mini 3 | October 22, 2014 | October 22, 2014 | 0 | Pangu8 | Pangu Team | |
| iPod touch (6th generation) | July 15, 2015 | July 16, 2015 | 1 | TaiG, PP Jailbreak | TaiG, PP Jailbreak | |
| iOS 9 | September 16, 2015 | October 14, 2015 | 28 | Pangu9 | Pangu Team | |
| iPhone 6S | September 25, 2015 | October 14, 2015 | 19 | Pangu9 | Pangu Team | |
| iPhone 6S Plus | September 25, 2015 | October 14, 2015 | 19 | Pangu9 | Pangu Team | |
| iPad Mini 4 | September 9, 2015 | October 14, 2015 | 35 | Pangu9 | Pangu Team | |
| iPad Pro | November 11, 2015 | March 11, 2016 | 121 | Pangu9 | Pangu Team | |
| Apple TV (4th generation) | September 9, 2015 | March 23, 2016 | 196 | Pangu9 | Pangu Team | |
| iPhone SE (1st generation) | March 31, 2016 | July 24, 2016 | 115 | PPJailbreak | PPJailbreak, Pangu Team | |
| iOS 10 | September 13, 2016 | December 28, 2016 | 15 | Yalu | Luca Todesco | |
| iOS 11 | September 19, 2017 | December 26, 2017 | 98 | LiberiOS | Jonathan Levin | |
| IOS 12 | September 17, 2018 | February 22, 2019 | 158 | unc0ver and checkra1n | Pwn20wnd, sbingner, Ian Beer, Brandon Azad, Jonathan Levin, PsychoTea, xerub, ninjaprawn, stek29 | |
| IOS 13 | September 19, 2019 | October 13, 2019 | 24 | unc0ver and checkra1n | Pwn20wnd, sbingner, Ian Beer, Brandon Azad, Jonathan Levin, PsychoTea, xerub, ninjaprawn, stek29 | |
| iOS 14 (beta) | June 22, 2020 | June 23, 2020 | 1[147] | checkra1n | qwertyoruiop, argp, axi0mX, danyl931, jaywalker, kirb, littlelailo, nitoTV, nullpixel, pimskeks, sbingner, Siguza |
Table of tools[edit]
RetroArch
RetroArch is a frontend app for game engines, emulators, and media players, offering you the tools needed to play classic games on your devices.
RetroArch is an easy app to use with a user-friendly interface that offers access to your game collection in an ordered manner. It works on multiple platforms and, as soon as you connect a common joypad to your device, it will be automatically recognized and configured. This provides you with a console experience right there on your iPhone or iPad. If that weren’t enough, you can also record any of your gaming sessions and enjoy new programs as they get added to RetroArch’s library on a regular basis. This emulator is free to use and works on all iOS devices.
Content Summary
How to Download RetroArch:
You won’t find this iOS console emulator in the iOS App Store because it isn’t the kind of app that Apple approves of. You can, however, get it by downloading TweakBox app installer and we’re going to show you how to do that. Tap to download directly.
Download Link 1
Download Link 2
Download Link 3
Method 1: iOS
- On your iOS device and download TweakBox app
- Find and tap the TweakBox app icon on your homepage to open it
- Tap Apps > TweakBox Apps
- Type the app name into the search bar and wait for the app to be found
- When it is found, tap on Install or click on the download button above
- Wait until the emulator has installed to your device and you can begin using it.
Method 2: Install IPA File
IPA File Link
- First, get the RetroArch .ipa file from above
- Download and install Cydia Impactor. Install the IPA.
Method 3: Android APK
Retroarch is an open-source project that is also available for Android users. Follow the download link below for more details.
Android APK
Both RetroArch and Libretro are the ideal programs for creating your own emulators, games, and even multimedia programs.
Note: RetroArch is what is known as ‘multi-versatile”. For you to do anything with it, you will require modular programs known as cores, and these do NOT come with the app. To get them, you must first go to Online Updater in the app itself and choose Core Updater – the cores will then be downloaded.
App Features:
- Choice of great looking menus
- Ability to scan directories and files and add them to the game system collection
- Once a game is added to a collection, see database information about it
- Download cores online
- Ability to update everything in-app
- Choice of Game and Watch games to download and play using the exclusive Game and Watch Emulator
- Input remapping built into the app
- Remap the controls
- Add and use cheats
- Support for multiple languages
- More than 80 cores available
- Use NetPlay for multiplayer gaming
- Save states
- Take screenshots
- No DRM
- Open-source program
- No usage restrictions
- No push ads
- Many more cool features
Alternative Emulators:
If you are looking for an emulator that plays specific console games, try one of these:
Retro Arch is set to become one of the leading apps for playing some of the classic console games through so download it and try it; for more updates, you can follow us on Facebook.
Fix RetroArch Errors:
Here are some common errors on the gaming platform, with possible solutions.
Fix Untrusted Developer Error:
One of the things that Apple does to try stopping you using unofficial apps is to show an Untrusted Developer error, and this is common with TweakBox. You can fix this and get into the app very easily:
- Open Settings and go to Profiles & Device Management in General
- Look for the app in the profile list and tap on it
- Trust the app and close Settings
- When you try RetroArch again, it will be fine
What’s New in the Install TweakBox on PC Archives?
Screen Shot
System Requirements for Install TweakBox on PC Archives
- First, download the Install TweakBox on PC Archives
-
You can download its setup from given links:


