VPN 360 app Archives

VPN 360 app Archives
Tag: VPN
The next phase of a post-COVID world will be one of reduced physical contact, tighter regulations, and new habits and hygiene practices. This will translate into significant process changes which will be deeply enabled by mobile technology. All mobile form factors will be more integrated into how we interact. Interactional changes will be found in our homes, offices, public spaces and services.
In this blog post I address two fundamental questions as a technologist on the underpinnings of this shift:
- How can enterprises find ways of rebuilding and cementing trusted relationships using mobile technology?
- How does our infrastructural foundations support mobile technology for contactless transactions? (privacy, two-factor authentication, data quality and so on)
Situational shift to mobile
Given the rapid shifts in the last six months in how we can interact with each other, enterprises will have to be agile and flexible in process design going forward to optimize opportunities for customer engagements.
We will continue to have further disruptions on how we live and work in the next 12 to 18 months and potentially beyond. Some of the shifts towards mobile have been expected for a while, yet this crisis has pushed the timeline ahead as to how we engage.
Use cases in the “new normal”
Here are some use case examples in this next phase of business where mobile enables the transaction between consumer and environment:
Education. Thereskilling and training certification that will be necessary to address unemployment, will be on Mobile First. Because of bandwidth, learner attention span, and form factor, there will be retooling of educational programs to be bite-sized and more media oriented.
Retail. Retail and delivery businesses shifting to remote first, with drop-off points that use mobile for contactless signatory and payment.
Healthcare. Telemedicine primarily by mobile devices (phone, laptop, phablet). Personal medical data sharing over mobile will require enhanced data encryption and two-factor authentication, which needs addressing via encryption and authentication.
Entrepreneurship. More side hustles that are mobile-based and mobile administered. Any authorization and transaction-oriented activities will be driven by mobile.
Government. Requests for document renewal or identity authentication for approval or submission of materials, with one-touch request.
Supply chain. Visibility and tracking of inbound and outbound materials. One-click reordering, and contactless payment verification.
Workplace. Contactless engagement with mobile as authentication of actions (coffee machine payment, copier usage, keyless office, meeting room allocation).
Facilities management. Hygiene controls with personnel health detail tracking (who cleans what room when). Deep cleaning management tools for audit trails, liability.
Role of mobile in creating engagement
Building trust
As we filter through the level of rubbish coming at us via social media, websites and our email, most of us are looking for a trusted information source. Our mobile is our window to the world, and many are applying appropriate filtration to make that world a bit more manageable.
The reason that people did previously download an app was partly based on what information had to be handed over in terms of permissions. The app builder needs to build a trusted relationship on benefit, not on what can be leveraged from the consumer.
To build that trust and create a closer engagement – albeit driven by situational need vs. consumer want – app developers need to consider these consumer needs:
- Level of trust in quality of information provided (e.g. weather info vs something more critical)
- Trust in app data usage and functionality (does it work?)
- Privacy of data being used and being held (statements and auditability)
- Location of data (on whose device: client or server)
- Speed and reaction time (Is there edge computing or the use of IoT to help push mobile information quickly?)
- Loss of data or loss of device and the impact on app access (More than lost passwords, lost processes and lost data)
Technological foundations for mobile usage
Network and bandwidth
We have all experienced bandwidth issues in the last few months, either sharing bandwidth with loved ones in lockdown to peak periods of video conferencing activity across geographic regions. Entertainment content providers such as Netflix and Disney+ were asked to lower the quality of the data streaming.
But then what online activity will take priority? Will we start to see pricing differentials for guarantees of availability? What about subscription models with platinum, gold and silver memberships (as in frequent flyer programmes) as to the network bandwidth you or your activity is allocated? Will things be done over VPN not only for privacy but for priority? I also see VPN as a possible solution towards issues like Zoom bombing and other intrusions to daily business operations.
We come to the role of a pandemic in 5G investment, which is similar to the role of investment in R&D during an economic downturn. Clearly, the world needs better bandwidth with more agility and future-proofed for functionality. You cannot drive a fast car on a bumpy road with potholes.
But for countries losing thousands of citizens to a virus with critical infrastructure at risk, where is the priority of a better telecom infrastructure? My colleague Shamir Amanullah wrote a report prior to the pandemic about the Race for 5G in Southeast Asia which is a good barometer for other regions. There is a good CNBC article from Todd Wassermann on the US situation, and a rather excellent survey on consumer sentiment on 5G from February 2020 by Politico.
Role of data quality and its security
Going back to my previous statement about rubbish and social media, the validation and quality of data exchange is part of the value proposition of using mobile technology.
What aspects of our current IT infrastructure create that ‘data value add’?
IoT and Edge Computing. Most of us are not going to be comfortable in crowds going forward. If I can reserve a space, or I can use a sensor to see how full an environment currently is, it will impact my decision to go somewhere. The faster that real-time information is processed and available, the better the outcome.
Blockchain technology is functioning enough to address the challenge of how to secure the data and prevent malicious cyber-attacks. This includes medical data hacking, supply chain theft, and other data-oriented safety issues on hygiene and product providence that we are experiencing now.
Final thoughts
At Ecosystm, we highlight how and where enterprises plan to invest and adopt technology while adding insights and expertise on to the use cases and trends. We are also able to reflect upon the agility of the same enterprises to make that technology investment count towards the next phase of their business model. In a post-COVID situation we see inventive ways enterprises are using technology. This is not only for societal benefit, but to make a difference in the marketplace. And mobile plays a key role in this next phase of engagements.
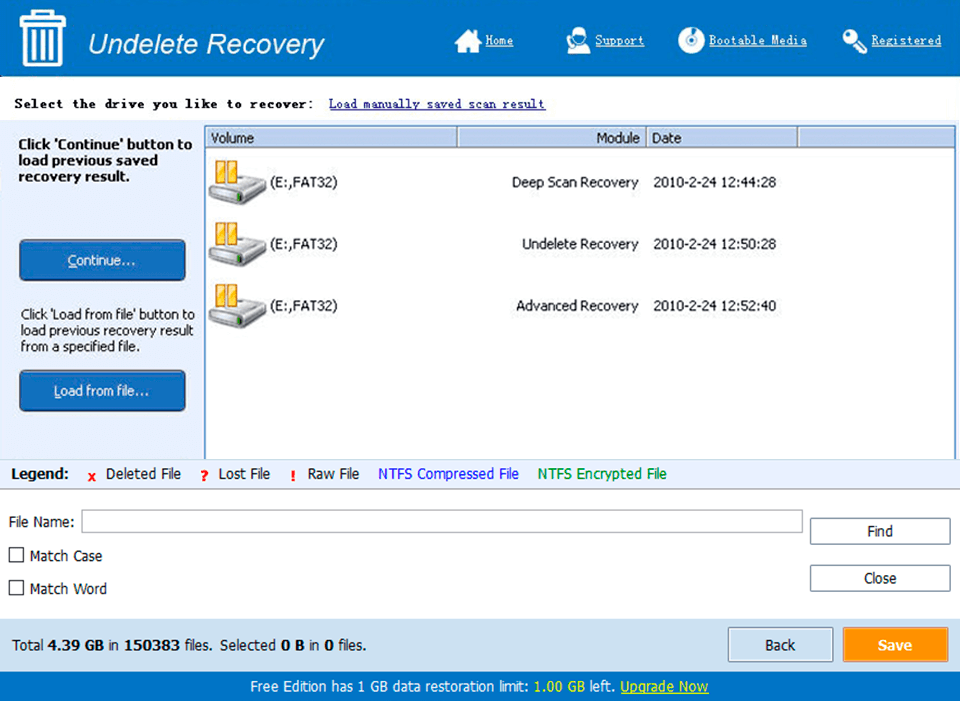
SysLog & Windows Event Log Archiving
EventLog Analyzer automatically archives all event logs and syslogs collected from Windows and UNIX devices, Routers & Switches, and other syslog devices on the EventLog Analyzer server itself. The event log archive is invaluable in forensic analysis and determining performance and usage statistics for a device.
Encrypting Archived Log files
Now, EventLog Analyzer encrypts the event log archive files to ensure the log data is secured for future forensic analysis, compliance and internal audits.
Hashing
The hashing of the archive log data files further secures the event log data.
Time stamping
The time stamping technique ensures that the archive data files are tamper proof. If there is a modification of file, this technique will reveal that the file has been tampered.
The three point security keeps the archive log data safe.
Configurable Log Archiving Intervals
The default log archiving interval creates a log archive file of the all the received raw logs every 24 hours. And these log archive files are then compressed (zipped) after every 7 days, to conserve hard disk space. You can configure the archive file creation and compressed file creation any time depending on how often you need to archive event logs. You can even disable log archiving entirely if needed.
Reports on Archived Event Logs
At any time, you can load event log archive file into the EventLog Analyzer database and generate reports from the archived event data.
Detailed Event Log Archiving
Every log archive file that is created, is stored along with the time of archive creation, size of the archive, and the device whose event logs have been archived. This makes it easy to load and generate reports from archived event logs.
Instant Event Log Archiving
EventLog Analyzer includes options to instantly generate log archives for all event logs collected so far. All event logs collected will be archived, irrespective of the log archiving interval defined. In this way, you can create and load archived files into the database at any time.

EventLog Analyzer archives network logs securely for future requirements.
Thanks!
Your download is in progress and it will be completed in just a few seconds!
If you face any issues, download manually here
The Blog
Some apps are known to interfere with the VPN’s normal work. We decided to publish our own list of known problems and solutions.

Windows Apps
► Qihoo 360, 360 Safeguard, 360 Total Security
Solution: Add Seed4.Me folder and files to antivirus exceptions, or replace Qihoo 360 with another antivirus.
How to add Seed4.Me folder to 360’s exceptions:
Open your 360 Total Security software > Click on Virus Scan > Click on Trust List > Add Directory “C:\Program Files\Seed4.Me VPN”.
Note: Seed4.Me re-installation may be required.
► TinyWall firewall
Solution: Allow LanTraffic + add Seed4.Me files to exceptions, if this doesn’t help, disable TinyWall.
According to the TinyWall developer, the problem was solved in the latest TinyWall versions.
► AnVir Task Manager
Solution: Add Seed4.Me folder and files to exceptions, or delete AnVir.
Android Apps
► NetGuard
Solution: Uninstall NetGuard.
Corporate Firewalls
► Fortinet FortiGate
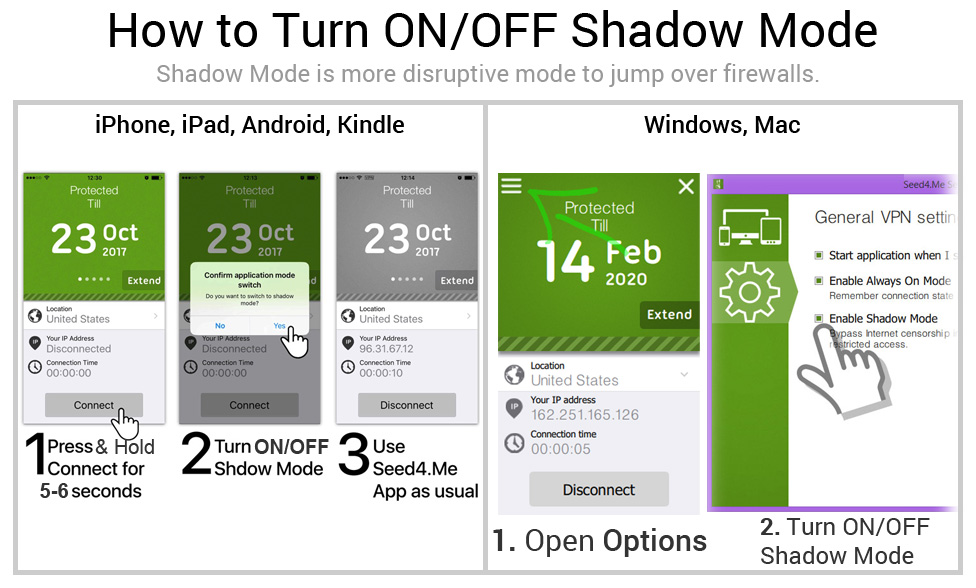
Solution: Try enabling Shadow Mode in Seed4.Me. Shadow Mode is a more disruptive mode to jump over firewalls.
Bonus: How to Properly Add Seed4.Me VPN to Antivirus Exceptions
Step 1. Temporary stop your antivirus
Step 2. Add the following folder to your antivirus exceptions:
C:\Program Files\Seed4.Me VPN
Step 3. Add the following files to your antivirus exceptions:
C:\Program Files\Seed4.Me VPN\bin\Seed4.Me_service.exe
C:\Program Files\Seed4.Me VPN\bin\Seed4.Me_VPN.exe
Step 4. Uninstall current (corrupted) Seed4.Me version
Step 5. Download and install the latest Seed4.Me VPN App
Step 6. Start antivirus software
Done!
Still nothing works? Don’t hesitate to contact our support team – support@seed4.me
What’s New in the VPN 360 app Archives?
Screen Shot
System Requirements for VPN 360 app Archives
- First, download the VPN 360 app Archives
-
You can download its setup from given links:


